Smart home cameras provide ease and better home monitoring, yet they also create genuine privacy worries as linked devices join daily routines. The main concern involves not just if hackers can break into a camera setup but also how camera construction, data protection, and user behaviors combine to form the degree of danger.
Understanding the Relationship Between Privacy and Smart Home Cameras
Smart home cameras have turned into key parts of current living, delivering comfort, protection, and links. Still, their broad use has also started vital talks about data privacy and digital safety.
The Integration of Smart Cameras in Modern Homes
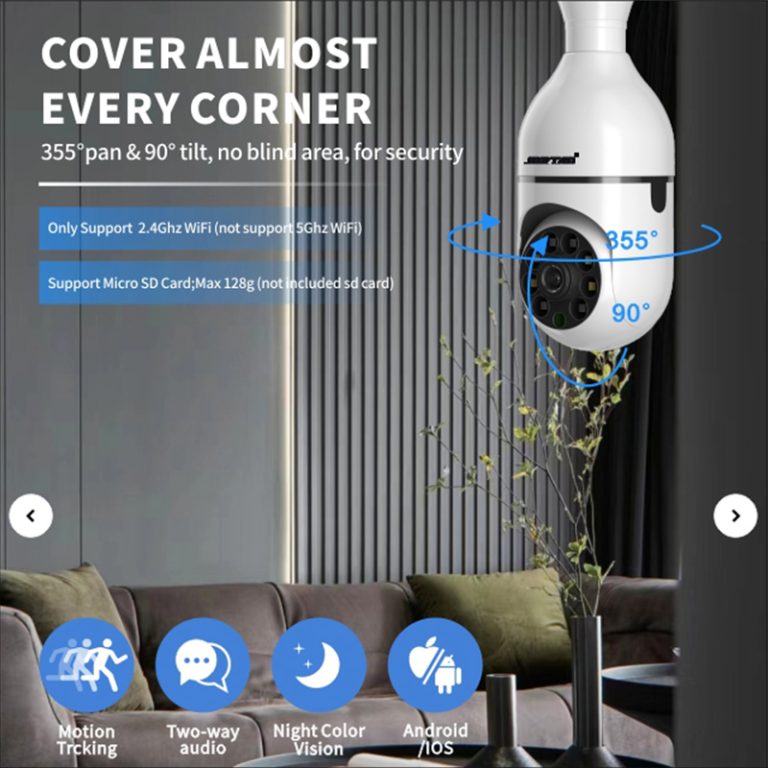
Thanks to progress in chips, software, and network tech, security cameras are slowly shifting from expert uses to the everyday buyer market, with more home WiFi cameras arriving in houses. This change has positioned smart cameras as main pieces in home automation setups. They link via Wi-Fi and cloud systems, letting users watch their homes from afar. After getting the app, people can check their workspaces and homes whenever and wherever. Such linking boosts ease but at the same time brings possible weak spots that outside attackers might use if security is lacking.
The Privacy Implications of Constant Surveillance
Non-stop video capture and sending mean that smart home cameras keep collecting heaps of personal details. When kept on cloud servers, this video might accidentally show private home facts. As a segment of smart home setups, smart cameras can gather image data in the home setting in real time, and they can examine and handle this data with aid from modern tech to offer users varied services. However, people often overlook how many private bits these recordings show—from usual habits to family dealings—which makes handling privacy a vital part of using connected gadgets wisely.
Common Security Risks Associated with Smart Home Cameras
While smart cameras improve safety, they also open fresh paths for online dangers if not set up or cared for correctly.
Vulnerabilities in Device Firmware and Software
Old firmware usually holds fixable issues that hackers can target to get unwanted entry. Many makers put off sharing fixes or neglect to alert buyers quickly about weak points. Poor starting settings, like default passwords from the factory or open ports, raise exposure dangers even more. Steady care matters a lot; so, check and tend to your camera often to make sure it runs well.
Risks from Network and Cloud Connectivity
Smart cameras depend on steady internet ties for live broadcasts and storage matching. Unsafe Wi-Fi setups let attackers grab video flows or change device options. In the same way, broken cloud accounts can cause unwanted views or spills of saved video. If coding standards fall short, even live views might get caught by bad actors.
How Hackers Breach Home Security Camera Systems
Online criminals use different ways to weaken linked watch systems. Knowing these approaches aids users in building better guards against break-in tries.
Exploiting Weak Passwords and Authentication Methods
Lots of users skip changing starting logins or repeat basic passwords over several sites. This carelessness makes force attacks simpler. Without two-step checks, unwanted sign-ins become easier too. Login stuffing—taking stolen passwords from other breaks—serves as another usual move that attackers apply to take over accounts.
Leveraging Malware and Botnets for Camera Access
Hackers at times send out bad software aimed at IoT gadgets like cameras to secure lasting, far-off control. After takeover, these gadgets might join bigger botnets for spreading denial-of-service (DDoS) strikes or hidden watch tasks. Tainted units could send user info quietly without any clear hint of takeover.
Protecting Privacy in Smart Home Camera Usage

To guard privacy well, home owners need to take active safety steps when setting up their smart camera systems.
Implementing Strong Security Practices at the User Level
Password Management and Authentication Controls: Users ought to always make special passwords mixing letters, numbers, and signs for each device login. Multi-step checks add an added shield by needing proof beyond only a password. Updating logins now and then cuts risks from past breaks.
Network Segmentation and Secure Connections: Putting IoT gadgets on a special network stops the spread of issues if one setup gets broken. Using WPA3 coding greatly boosts Wi-Fi safety. Turning off far-off entry when not needed shrinks possible attack paths.
Ensuring Device and Firmware Integrity
Regular Updates and Vendor Support Evaluation: Firmware fixes cover known weak spots; thus, planning routine updates straight from checked maker sources proves vital. Picking brands that keep clear safety rules guarantees continued guard against new dangers.
Monitoring Device Activity for Anomalies: Users should look over link records often to spot odd sign-in tries or strange IP spots reaching their systems. Network watch tools can aid in finding unwanted actions early, so fixing steps—like restarting gadgets—can happen right away.
For instance, Jortan stresses careful use by adding solid coding rules into its camera systems: Jortan protects people’s privacy by only capturing the moments they care about—recording only when motion is sensed, the alarm triggers, or the user commands it—and then encrypts the clips so only account users have access.
The Role of Manufacturers and Regulators in Safeguarding User Privacy
Makers hold an important spot in forming how safe smart home networks work, while rule-makers push following rules through policy setups. Business rules now set basic needs for coding power, check systems, and fair data care in IoT goods. Approval plans push sticking to safe build ideas before items hit buyers.
On top of that, worldwide rules like GDPR in Europe or CCPA in California demand firms get clear user okay before gathering personal info and require open sharing about keeping policies. These law setups boost answerability while growing public faith in linked tech.
Future Directions in Smart Home Camera Security
The coming wave of smart cameras will probably center on building firmer privacy-saving traits right into hardware builds instead of counting only on cloud fixes.
With quick growth in tech like the Internet of Things and artificial intelligence, the smart home field is growing fast. On-gadget AI handling allows instant review without sending touchy video outside, cutting exposure dangers a lot. Full-end coding makes sure that only allowed people can reach saved stuff no matter where it sits.
User learning will stay key too, since knowledge right away shapes safe setup ways among final users. Groups keep starting plans aimed at showing right setup skills—for example, making sure firmware fixes go on quickly—to shrink weak times by a good deal.
To check out better models built with improved privacy rules and smart spot skills like two-way video talk for family watch cases noted above (old one-way video watch models no longer fit this rising market need), readers might think about viewing the Jortan Camera Series.
FAQ
Q1: How do I know if my home security camera has been hacked?
A1: Signs include unexpected movement alerts when no motion occurred, unknown IP addresses accessing your device logs, or performance drops caused by background transmissions.
Q2: Are cloud-based storage options safe for my video footage?
A2: Cloud storage can be secure if providers implement strong encryption standards; however, users should still review privacy policies carefully before enabling automatic uploads.
Q3: What’s the best way to prevent future hacking attempts?
A3: Always update firmware promptly, use complex unique passwords with two-factor authentication enabled, isolate IoT devices on separate networks, and purchase equipment only from trusted vendors offering transparent support policies like those recommended by Jortan.